Author: Tim Higgins
Review Date: 7/10/2001
![]()

| Pros: | – Built-in Windows / LPR print server. – Supports dialup WAN connection with auto-failover – Protects against common hack exploits – Good speed – Access control by time of day |
| Cons: | – Poor logging features – No email alerts of hack attempts – Unhelpful on-line help. |
| Review Updates 2/28/02 Make sure you check the part number on your Barricade 7004ABR before you download new drivers. Drivers are slightly different for different versions of the product. 10/29/01 Official firmware 1.40 upgrade is available from SMC. 10/12/01 Reader reports indicate the firmward upgrades have fixed the several faults we found, review has been updated. 10/4/01 1.40 firmware upgrade available . We’ve got reports that this will likely fix the router’s problems with PTPP connections 7/11/01 Added firmware revision info. |
The Basics |
|
Introduction
The SMC7004ABR is a remodeled version of SMC’s Barricade that is replacing the “BR” designated model. The changes aren’t completely transparent, however, and I found both positive and negative surprises.
What’s Different
If you’re unfamiliar with what the Barricade can do, check the Product Guide details page, or the reviews of the earlier model, or its Asante twin. I’m going to focus mainly on the differences between the older and newer versions.
You’d think that SMC would have taken the opportunity to use a more attractive design for the enclosure, but the Barricade is still pretty much the same homely little gray box. It’s slightly wider, the LEDs have been moved to the front of the box and are much easier to see, a reset button has been added, and the power switch removed. The connector layout is the same, however, with WAN Ethernet, serial, and printer ports on the rear and LAN ports on the front. A welcome improvement is the fact that the LAN ports are now auto MDI/MDI-X sensing. This feature, which seems to becoming standard on new routers eliminates the need for both crossover cables and “uplink” ports, and gets you reliably connected to whatever piece of Ethernet gear you connect it to. SMC has also changed the Admin page address to 192.168.2.1. and changed the login to require a User Name (which you can’t change) but no password (I suggest you enter a strong password as part of your ABR setup).
The big surprise is that the ABR has an entirely new circuit design, including a change from 16 bit x86 to 32 bit ARM (RISC) processor. This means a new firmware base has been established and firmware releases for the old Barricade can’t be used in the ABR!
Adds and Deletes
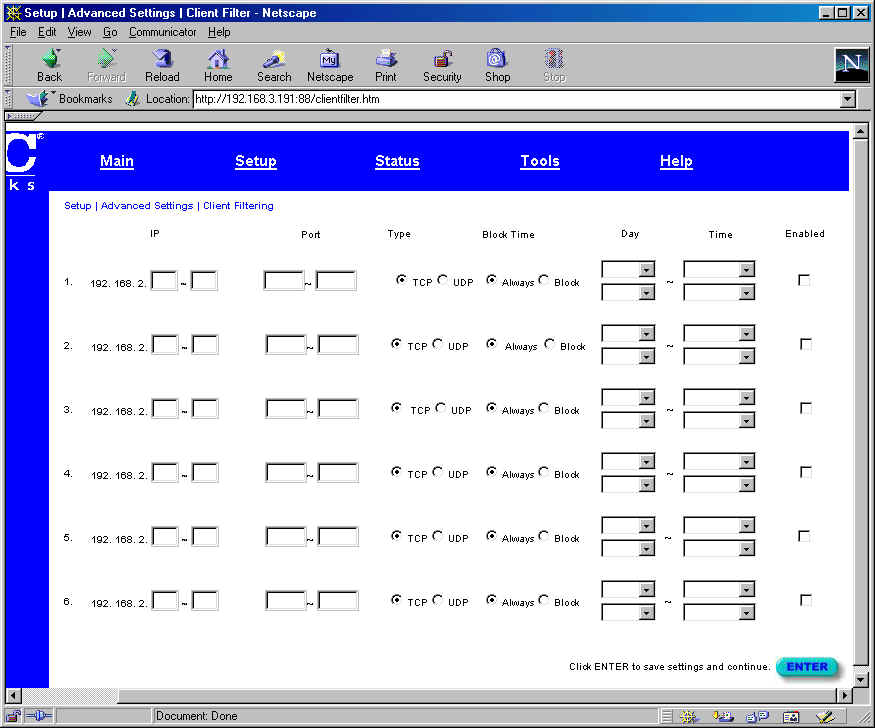
The screen shots above show two of the most significant changes, i.e. the Security Log feature (you can see some port scan log entries, both before and after the Real Time Clock was properly set) and Time of Day based Access controls. The new admin interface is organized differently and tends to not scale very well to the width of the open browser window. Each page has an Enter button that saves your entries but also advances you to the next page in the sequence. I also had problems opening the admin page with Netscape 4.75 (I got a “connection reset by peer”), but everything worked fine with IE 5.0.
TIP: The admin webserver actually runs on Port 88, but your browser should be automatically redirected if you just type in the 192.168.2.1 address. I found that entering http://192.168.2.1:88/ got me past the Netscape problem.
Here’s a summary of the other changes that I found from the BR to ABR:
Features Added:
NTP based real time clock, which automatically finds a Network Time server at router bootup (you can’t control which one), and sets the clock. You just have to tell it what time zone you’re in.
Access Control by Time of Day. You can block access to ranges of ports for ranges of IP addresses either always or for certain times of the day and days of the week. You also get six sets of Access controls vs. four in the BR.
Dialup Auto Failover – The serial port can now automatically start a dial-up or ISDN connection via the built-in serial port when the Broadband WAN connection goes down and restore the Broadband connection when it returns.
Virtual Server Public and Private ports – All Virtual Servers can now have both their “Public”, i.e. Internet, and “Private”, i.e. LAN ports specified. This allows you to have your FTP or other server accessed from whatever Public port you want.
“Hacker Attack” monitoring and logging – See the comments below.
No rebooting when changing admin settings.
Features Removed:
Router status without login – Although some may disagree, this is a good thing and enhances security. If you try to access the admin screens, you get a standard Windows authentication pop-up box.
Virtual Server “Loopback” – This is the ability to reach Virtual servers from LAN machines by using the router WAN address.
Useful Help screens – The on-line Help is little more than a glossary of terms, some elementary Troubleshooting tips, and SMC Tech support info.
Non standard FTP port – But no longer needed due to the ability to specify all Virtual Server Public and Private ports.
More Work Needed
Since changing processor architectures meant re-implementing all Barricade features, some old features didn’t make the transition very well, and there are new features that will need some more work.
The new “Hacker Attack” features fall into the “Needs Work” category. SMC looks like it’s attempting to add SPI-like (Stateful Packet Inspection) features, but not going as far as to say that the ABR is an SPI based router. When enabled, this feature is supposed to protect against and log the following attacks: IP Spoofing, Land Attack, Ping of Death, IP with zero length, Smurf Attack, UDP port loopback, Snork Attack, TCP null scan, and TCP SYN flooding. But when I ran some simple TCP port scans against the ABR, it logged only the scan on port 88! Huh? Port scans are probably the most common and widely known “hack attack”. Why aren’t they logged (especially since the old Barricade did)? The ABR was properly secured however, returning no response to any of the scans. I didn’t run any of the attacks listed above, though, so can’t comment on the protection that the ABR provides.
Routers with “SPI” features usually provide a way to email notice of an attack, but the ABR doesn’t. It doesn’t even auto-refresh the browser screen if you have the Status page (that contains the Security Log) up and a hack is detected and logged. There’s also no way to clear or save the logs and no on-line Help to aid in deciphering what the log is telling you.
While I’m ranting about logging, I might as well finish the job! I’ve long felt that the Barricade’s logging features have been perhaps its weakest point, and the ABR has taken a step back in this area. As mentioned above, system events such as WAN DHCP leases, dialup and PPPoE connection sessions and router print jobs are nowhere to be found! And there’s still no traffic (Web site visit) logging or support for detailed logging via syslog or SNMP traps. C’mon guys, the competition is ahead of you here and widening the gap!
Finally, I found the Status page wasn’t much help when I was trying to check out the dialup auto-failover feature. I discovered that dialup connection sessions aren’t logged and the Status page doesn’t always show the status of the serial port. Instead, it changes the “Internet” Status between Cable/DSL and Modem. Granted, I was trying to check this out while switching one modem back and forth between my main dial-up router that provides my Internet connection and the ABR… not really a situation that would normally be encountered. But on the other hand, there’s no way to test whether the modem is connected and ready for action or to force the connection over to dialup for testing or other purposes either.
Router Performance
I ran the Qcheck suite to check the ABR’s performance and also upgraded my old “BR” with 1.92e firmware and ran the same tests so that I could compare old and new.
(Details of how I use Qcheck for router testing can be found here.)
Firmware/Driver Version: | Boot: V1.0 Runtime: V1.10 |
Test Description | Qcheck TCP Transfer Rate (Mbps) [1Mbyte data size] | |
BR (Old) | ABR (New) | |
WAN – LAN | 4.8 | 3.8 |
LAN – WAN | 4.3 | 3.5 |
Comments: I was surprised to find that the new RISC processor based platform had slower routing speed. The ABR numbers above are with the “hack alert” features enabled. Disabling the feature moved the throughput up to about 4Mbps. Even with the slower speed, however, you still have plenty of performance for most any broadband connection.
Test Description | Qcheck Response Time (msec) [10 iterations 100byte data size] | |
BR (Old) | ABR (New) | |
WAN – LAN | 4 (avg) | 5 (avg) |
LAN – WAN | 4 (avg) | 4 (avg) |
Comments: No significant differences here.
Test Description | Qcheck UDP stream | |||
(Actual throughput- kbps) | (Lost data- %) | |||
BR (Old) | ABR (New) | BR (Old) | ABR (New) | |
WAN – LAN | 485 | 314 | 1% | 37% |
LAN – WAN | 488 | 310 | 2% | 38% |
Comments: UDP streaming performance takes a significant hit in the new model, with the router well into overload at a 500kbps UDP stream rate. This result means you may need to switch to a lower rate if you regularly watch fast Internet video streams.
Summary
In spite of all my complaining, and all things considered, I think SMC did a pretty good job on the update of one of the best router values available, and I’m adding the ABR to the Practically Recommended list. If SMC is true to form, they’ll fix many of the bugs and omissions I’ve seen and continue to enhance the ABR’s value (and feature set) with regular firmware updates.




